Frequently asked questions
We host zero logging DNS servers with support for DNS-over-HTTPS (DoH) & DNS-over-TLS (DoT). Our servers blocks ads, malware, trackers, viruses and telemetry.
Behind this website, and the related services, is a single computer enthusiast who like to tinker with servers, code and similar things at his free time. There’s thus no corporation behind this website and the only source if income (if any) is based on donations.
Best way to contact me is on Telegram: https://t.me/NoExitTV
All our dns servers use the blocklist oisd.nl. The exact link to the blocklist we use is: https://dbl.oisd.nl
We really appreciate the work that sjhgvr have put into the blocklist.
All our DNS servers use the following whitelists:
https://raw.githubusercontent.com/AhaDNS/Aha.Dns.Domains/master/Domains/whitelist.txt https://raw.githubusercontent.com/anudeepND/whitelist/master/domains/whitelist.txt
Each AhaDNS server host its own, local, recursive DNS using unbound. This is done to minimize the amount of trust we have to put in others.
The only source of income for AhaDNS is from donations.
Other than this, Fredrik funds everything from his own pocket.
Netherlands server is hosted at LiteServer.nl
India server is hosted at Linode.com
I often get requests from people wanting to help out with managing the servers. Right now I do not allow anyone other than myself access to them due to privacy and security concerns.
If you enjoy what AhaDNS has to offer and want to help out, you can always donate any amount to help out with the server costs.
Another great way to help out and keep AhaDNS active is to spread the word about us on other websites and forums.
It’s also always fun if you want to participate in the discussion we have in our Telegram discussion group at: https://t.me/ahadns_community
Do you own/operate hardware and want to host a AhaDNS VM? Then contact us a we’ll talk more.
We see AhaDNS as a complement to web browser ad blockers.
Most of us use some form of ad blocker in our web browser. These can only block ads that you receive while using the web browser to brows the web. What about windows telemetry? Smart home (IoT) device telemetry? Ads in smartphone apps? Ad blocking for your entire network? This is where AhaDNS can help. By setting your router or your devices to use our DNS servers, ads, malware, trackers, viruses and telemetry will automatically be blocked!
If you would like a website to be unblocked, you can fill in our white-list request form at https://ahadns.com/whitelist-request/. If the request is approved, then the submitted domain will automatically be added to our custom white list. This list is automatically propagated to all our DNS servers.
We do not log or store any personal DNS request data. This means that we don’t know anything about what requests a specific user have made. We do keep some anonymized statistics over each server, containing data such as, but not limited to, total number of DNS requests, total number of DNS requests blocked, type of DNS query (A, AAA, CNAME etc) and type of answer (NOERROR, NXDOMAIN, NODATA etc). These statistics can be seen at https://statistics.ahadns.com/. The statistics do not contain any information about the content of the DNS request, such as the domain requested, or the requesting IP address.
Our statistics are collected from the utility unbound-control on each DNS server with extended statistics turned on.
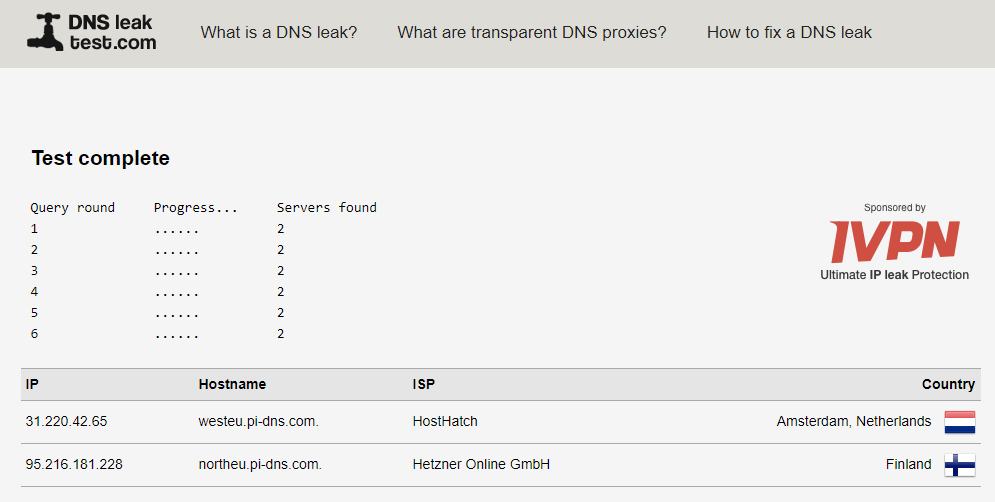
Visit the test site dnsleaktest.com and click “Extended Test”.
When the test is complete, the only dns servers visible should be the AhaDNS servers that you’ve selected to use when configuring your device.
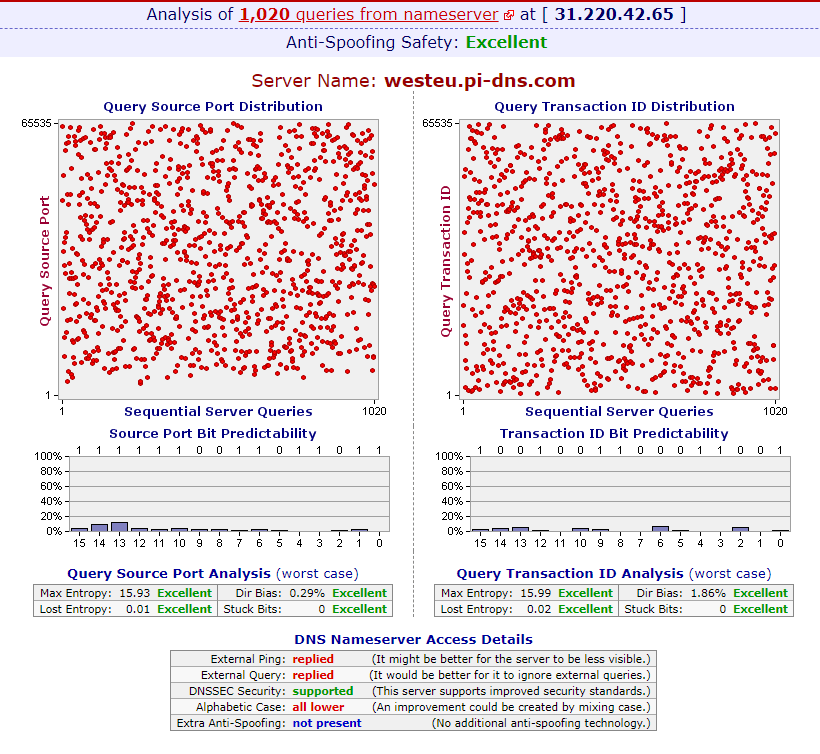
All our servers are tested for chache poisoning using the DNS Nameserver Spoofability Test by GRC and have passed with an excellent anti-spoofing safety.
Yes, all our DNS servers apply QNAME minimization.
No, our DNS servers does not send EDNS client subnet information.
You can test it with this command:
dig @5.2.75.75 txt o-o.myaddr.l.google.com +short
Compare that to google’s DNS server:
dig @8.8.8.8 txt o-o.myaddr.l.google.com +short
Yes they do. If the domain “domain.com” is in our block-list, our DNS servers will also block any subdomain to that domain. Meaning that “*.domain.com” also will be blocked.
We’ve automated the entire server setup process using Ansible. You can easily use the same script to setup your own AhaDNS server.
See: https://github.com/AhaDNS/dns-server-setup
We recommend you to create the server at any of our sponsors since the script have been verified to work there.